Z7 Cyber Intelligence
Most Dangerous Cybercrime Groups
Executive Intelligence Series
Ransomware operations no longer function as isolated criminal gangs. They operate as mature, adaptive ecosystems sharing infrastructure, personnel, and tactics across campaigns and regions.

Intellexa
Commercial Spyware Intelligence Brief
Intellexa represents one of the most controversial and opaque actors in the global surveillance ecosystem, operating at the intersection of commercial spyware, state-level intelligence collection, and human rights risk.
CLASSIFICATION
CRITICAL THREAT
The SitusAMC Breach
Vendor Risk Intelligence Brief
The SitusAMC incident exposed a critical reality facing financial institutions: security failures within trusted third-party vendors can produce systemic risk without a single bank system being directly breached.
CLASSIFICATION
CRITICAL RISK
Commercial Spyware Landscape 2025
Global Threat Intelligence Report
The mercenary spyware industry faces unprecedented legal pressure alongside continued proliferation. NSO Group’s landmark $168M loss established critical precedent. Nation-state APTs achieved historic breaches including North Korea’s $1.5 billion Bybit heist and China’s Salt Typhoon infiltration of US telecommunications.

Akira Ransomware
Threat Actor Intelligence | Most Dangerous Cybercrime Groups
CLASSIFICATION
CRITICAL THREAT

ALPHV / BlackCat
Threat Actor Intelligence | Most Dangerous Cybercrime Groups
CLASSIFICATION
CRITICAL THREAT (DEFUNCT)

Lockbit
Most Dangerous Cybercrime Groups – 2025
Once the most prolific ransomware operation in the world, LockBit reshaped the ransomware economy before becoming the target of one of the most coordinated international law enforcement takedowns to date.
CLASSIFICATION
CRITICAL THREAT (DEGRADED)

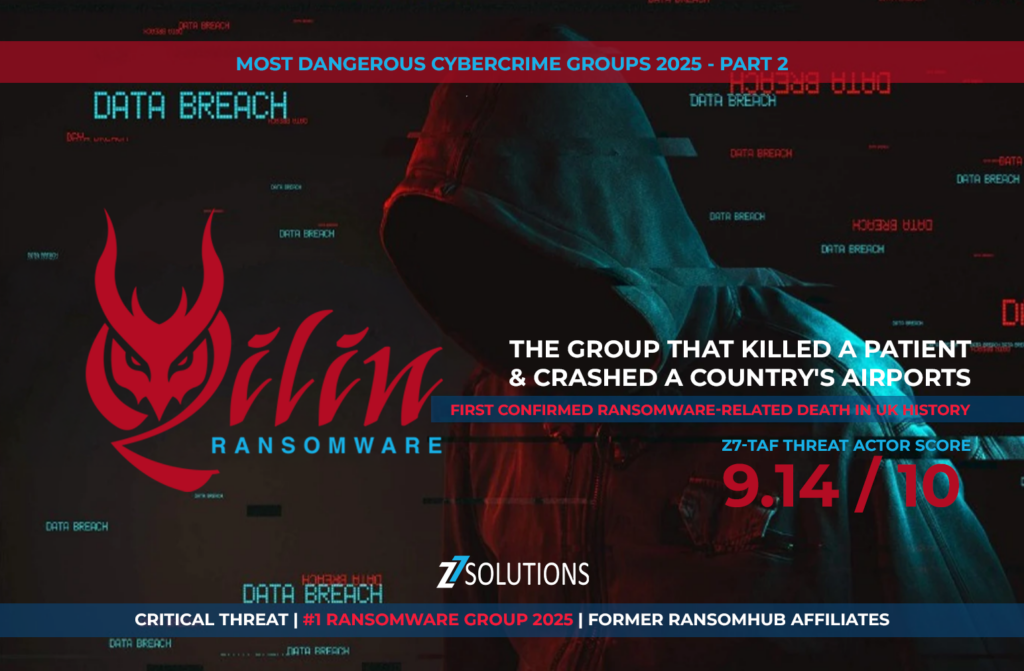
Qilin
Threat Intelligence Preview | Most Dangerous Cybercrime Groups
Qilin represents a dangerous escalation in ransomware operations — crossing from financial disruption into confirmed real-world harm. Its activity has redefined the human impact of cybercrime and raised urgent questions for healthcare, pharmaceutical, government, and financial institutions.
CLASSIFICATION
CRITICAL THREAT
Qilin Part 2
Most Dangerous Cybercrime Groups – 2025
Qilin (formerly Agenda) emerged as the world’s most prolific ransomware operation in 2025, capturing 29% of the global market with over 701 confirmed victims through October. Operating a sophisticated Ransomware-as-a-Service (RaaS) model from a Russian base, the group has demonstrated unprecedented escalation, including the first confirmed UK ransomware fatality.
CLASSIFICATION
CRITICAL THREAT
Odyssey Stealer
Threat Intelligence Deep Dive | Cyber Intelligence Division
Odyssey Stealer is a high-threat macOS information stealer that has evolved from the Atomic Stealer (AMOS) and Poseidon Stealer lineages. Authored by a threat actor known as “Rodrigo” (Rodrigo4), it operates as a Malware-as-a-Service (MaaS) for approximately $3,000 per month. As of February 2026, it has transitioned from a data exfiltration tool into a sophisticated Remote Access Trojan (RAT) with a global reach.
CLASSIFICATION
HIGH

Intellexa Part 2
Commercial Spyware Intelligence Brief
This intelligence report details the resilience and evolution of Predator, a commercial spyware suite developed by the Intellexa Consortium. Despite heavy international sanctions, criminal prosecutions in Greece, and a massive data leak in December 2025, Predator remains active and technically superior as of February 2026. The report highlights a fundamental shift in the spyware market from a foreign-owned proliferation threat to an American-invested procurement opportunity.
Quantum Era
Quantum Computing Threats and Post-Quantum Cryptography Readiness Intelligence Assessment
This February 2026 assessment by Z7 Solutions details the rapidly accelerating threat posed by quantum computing to current cryptographic standards and the urgent need for Post-Quantum Cryptography (PQC) migration. The report highlights a critical “migration timeline gap,” where large enterprise PQC transitions are estimated to take 12–15+ years, while a Cryptographically Relevant Quantum Computer (CRQC) could arrive as early as 2030–2040.

Raas
Z7 Cyber Intelligence | Executive Briefing
Takedowns of ALPHV and LockBit eliminated 40% of the market, yet ransomware attacks reached historic highs. Download the definitive 100+ page Z7 intelligence briefing.

Scattered Spider
Most Dangerous Cybercrime Groups – 2025 | Part 2
Scattered Spider demonstrates how sophisticated social engineering can outperform advanced malware. By exploiting human trust rather than technical vulnerabilities, this group has caused prolonged outages and substantial financial losses across retail, hospitality, and cloud service ecosystems.
CLASSIFICATION
CRITICAL THREAT
Book Your Free IT Strategy Session
Stop settling for slow networks and reactive support. Let’s map out a proactive plan to keep your business running at peak performance.